The Phantom Network Problem
Imagine discovering your second-hand iPhone is locked to a network that vanished five years ago. No customer service number works, no website exists, and Apple shrugs when you ask for help. Welcome to the world of ghost network locks – a digital purgatory affecting millions of UK devices.
These phantom locks persist because iPhone carrier restrictions are burned into the device's firmware during manufacturing. When networks disappear through merger, acquisition, or bankruptcy, their locks remain active indefinitely. Your iPhone doesn't know its original jailer has ceased to exist.
The Merger Massacre: Where Networks Go to Die
UK telecoms history is littered with absorbed brands whose iPhone locks still haunt the second-hand market. Each merger creates thousands of orphaned devices locked to networks that officially no longer exist.
Orange UK: The Biggest Ghost of All
Orange UK disappeared in 2012 when Everything Everywhere (now EE) absorbed the brand. However, millions of iPhones remain locked to "Orange UK" in Apple's database.
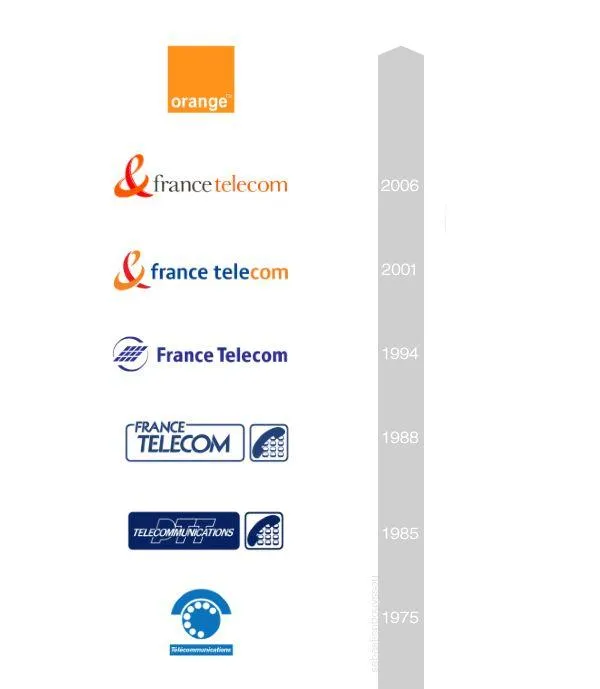 Photo: Orange UK, via logodix.com
Photo: Orange UK, via logodix.com
These devices display "Orange" in settings but can't connect to any current UK network. EE officially denies responsibility, claiming Orange locks predate their acquisition. Meanwhile, owners are trapped with expensive paperweights.
Current Status: EE sometimes unlocks Orange devices "as a goodwill gesture" but has no obligation to do so.
T-Mobile UK: The Silent Killer
T-Mobile UK suffered the same fate as Orange, absorbed into EE in 2012. T-Mobile iPhone locks are particularly problematic because the brand continues operating in other countries, confusing Apple's unlock systems.
 Photo: T-Mobile UK, via logodix.com
Photo: T-Mobile UK, via logodix.com
Devices locked to "T-Mobile UK" often get rejected by Apple's automated unlock tools, which can't distinguish between the defunct UK operation and active international T-Mobile networks.
Current Status: EE handles some T-Mobile unlock requests but maintains no official policy.
Virgin Mobile: The Franchise Phantom
Virgin Mobile operated as an MVNO (virtual network) using other carriers' infrastructure. When Virgin's mobile license ended, they left behind thousands of locked iPhones with no clear ownership chain.
Virgin Media (the broadband company) insists they're unrelated to the old mobile operation. The original Virgin Mobile infrastructure was sold to EE, but EE denies inheriting unlock obligations.
Current Status: Complete bureaucratic void with no responsible party.
The MVNO Graveyard
Mobile Virtual Network Operators (MVNOs) are particularly dangerous for iPhone buyers. These companies rent network access from major carriers but handle their own customer relationships. When they collapse, unlock responsibilities vanish with them.
Blyk: The Youth Network That Died Young
Blyk targeted teenagers with "free" mobile service funded by advertising. They locked thousands of iPhones before collapsing in 2009, leaving young customers stranded.
Blyk's infrastructure was provided by Orange, but Orange refused to inherit unlock obligations when Blyk folded.
Ovivo: The Free Lunch That Wasn't
Ovivo offered "free" iPhone contracts with severe usage restrictions. When their business model failed, they disappeared overnight, abandoning customers mid-contract.
Devices locked to Ovivo show no network connection and cannot be unlocked through any official channel.
The International Confusion Matrix
Some ghost locks stem from international networks that operated briefly in the UK market before withdrawing.
Hutchison 3G (Pre-Three)
Before becoming "Three," Hutchison operated as "Hutchison 3G UK." Early iPhones locked to this network identifier often can't be unlocked by current Three customer service, who claim no knowledge of the old system.
Orange Business Services
Separate from consumer Orange, this B2B operation sold corporate iPhones with different lock identifiers. When EE absorbed Orange, business service locks were excluded from the transfer.
The Legal Black Hole
When networks disappear, unlock obligations enter a legal grey area. UK law requires networks to provide unlocks, but what happens when the network ceases to exist?
The Regulatory Gap:
- Ofcom's rules apply to active licence holders
- Merged entities deny inheriting unlock duties
- Liquidated companies have no assets to pursue
- Apple claims locks are "network responsibility"
Identifying Ghost Network Locks
Before buying any second-hand iPhone, check for phantom network locks:
Settings Check:
- Settings > General > About > Network
- Look for defunct network names
- Cross-reference with current UK operators
Common Ghost Network Identifiers:
- Orange UK
- T-Mobile UK
- Virgin Mobile UK
- Blyk
- Ovivo
- Hutchison 3G
- Orange Business Services
The Successor Responsibility Game
Some successor networks accept unlock requests for absorbed brands, but policies vary wildly:
EE (Orange/T-Mobile successor):
- Occasionally unlocks as "goodwill gesture"
- No official policy or guarantee
- Requires proof of original purchase
- Often demands payment despite legal obligations
Three (Hutchison successor):
- Generally refuses pre-Three locks
- Claims "different company" status
- Refers customers to Apple (who refuse)
Third-Party Liberation Routes
When official channels fail, alternative unlock methods exist:
Apple Direct Unlock Requests
Apple sometimes removes ghost network locks when presented with proof of legitimate ownership:
Required Documentation:
- Original purchase receipt
- Proof of network closure/merger
- Government-issued ID
- Written statement of circumstances
Success Rate: Approximately 30% for clear-cut cases
Professional Unlock Services
Legitimate unlock specialists maintain databases of ghost network bypass codes:
Reputable Services:
- Doctor SIM
- Unlock Base
- Direct Unlocks
Cost: £15-50 depending on network and device Success Rate: 70-85% for common ghost locks
The Nuclear Option: Hardware Modification
Extreme cases may require baseband modification – essentially reprogramming the iPhone's cellular firmware. This:
- Voids warranty permanently
- Requires specialist equipment
- Costs £100-200
- Carries risk of device damage
- May violate carrier agreements
Prevention: Ghost-Proofing Your Purchase
Avoid ghost network locks entirely:
Pre-Purchase Checks:
- Verify current network in device settings
- Test SIM card from intended network
- Research network history and mergers
- Demand seller warranty on unlock status
Safe Purchase Sources:
- Apple Store (always unlocked)
- Current network operators
- Established retailers with return policies
- CEX (tests and guarantees unlock status)
The Regulatory Solution
Ofcom is slowly addressing ghost network locks through new regulations:
Proposed Changes:
- Successor liability for unlock obligations
- Mandatory unlock databases for merged entities
- Apple cooperation requirements
- Consumer compensation schemes
Timeline: Implementation expected 2025-2026
What to Do Right Now
If you own a ghost network locked iPhone:
Immediate Actions:
- Document your device's lock status
- Gather any original purchase evidence
- Contact the successor network first
- Escalate to Apple if network refuses
- Consider professional unlock services
Long-Term Strategy:
- Monitor Ofcom regulatory changes
- Join consumer action groups
- Document all unlock attempts
- Consider small claims court for valuable devices
The Bottom Line
Ghost network locks represent a massive failure of UK telecoms regulation. Millions of perfectly functional iPhones remain artificially crippled by the digital ghosts of dead networks.
While waiting for regulatory solutions, affected owners must navigate a maze of successor denials, Apple buck-passing, and third-party services of varying legitimacy.
The lesson for future purchases is clear: verify unlock status before buying, and avoid devices showing any network other than current UK operators. In the world of ghost network locks, prevention truly is better than cure.
Your iPhone shouldn't be haunted by the failures of UK telecoms history. But until regulators force accountability, millions of devices remain trapped in digital limbo – locked to networks that exist only in firmware memory.


